Added benefits through connection to the Azure Active Directory
The basis for this simplification is the connection to a corresponding Azure AD group, via which certificates can be requested for all members of this group during the user import and also revoked again if required. But this connection also makes it possible to activate or deactivate further functions for the members of the respective group.
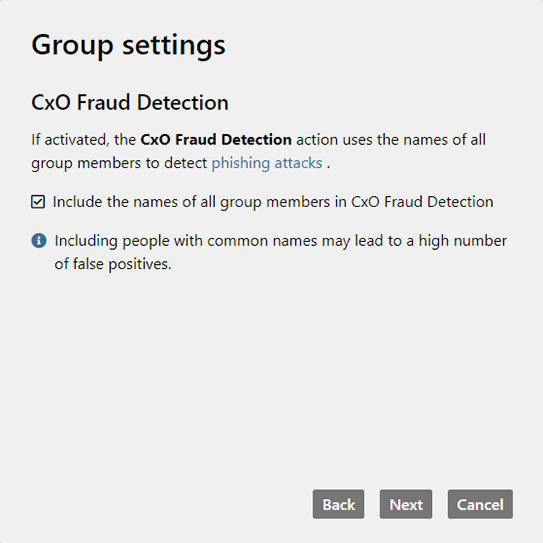
CxO Fraud Detection can be enabled for groups
CxO Fraud is also known as CEO Fraud and Fake President Fraud (FPF). In this type of fraud, attackers impersonate a company’s supervisors or other decision-makers and trick a company’s employees into transferring money to their accounts. In some cases, the identity of the employee’s own supervisor is faked; in other cases, the identity of a customer or supplier is faked, for example, in order to send supposed invoices in the customer’s name.
The CxO Fraud Detection in NoSpamProxy Cloud makes it possible to detect these attacks. In addition to rigorous evaluation of sender reputation based on SPF, DKIM and DMARC, CxO Fraud Detection compares the sender name from ‘Header-From’ and ‘MAIL FROM’ in inbound emails with the names of company users. This intercepts fake emails sent to you in the name of superiors or employees.
To enable CxO Fraud Detection, you simply need to enable it with one click during the configuration of Automatic User Import via Azure Active Directory.
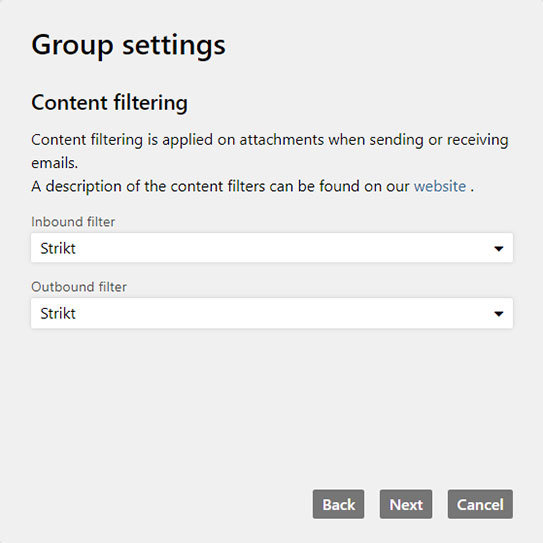
Configure content filtering based on groups
The content filter in NoSpamProxy Cloud fends off dangerous attachments unerringly. Depending on the selected filter and the respective file type the email is either rejected, the attachment is removed or the attachment is allowed.
With the December update, it is now possible to configure this setting individually for individual Active Directory groups. In this case, too, you simply need to perform a few clicks during the configuration of the Automatic User Import via Azure Active Directory.
Additional new features in NoSpamProxy Cloud
In addition to the connection to Azure Active Directory and the group-based configuration of Managed Certificates, CxO Fraud Detection and the content filter made possible by this, the December update of NoSpamProxy Cloud brings the following new features:
Support for S/MIME 4.0
From now on, NoSpamProxy Cloud supports the use of S/MIME certificates in version 4.0 according to the specification in RFC 8551.
New MIME types in the content filter
All content filters now account for Microsoft shell link (LNK and URL) MIME types as well as numerous OpenDocument formats such as ODS, ODT and ODP. The strict content filter now takes JavaScript files of the *.js pattern into account, the medium content filter now takes private certificates (.pfx, .p12) into account.
Not yet using NoSpamProxy?
With NoSpamProxy you reliably protect your company against cyber attacks. Request your free trial version now!